
4.6 (415) · $ 1267.00 · In stock
Description
Made with Fine Piqué Cotton. Soft, Smooth hair-less texture. Regular Fit, sits comfortably on the body. Contrast Collar with a neat birds-eye structure & a double placket. Durable ribbed cuff at sleeves. Regains shape, no end-of-day bagginess. High quality dying to achieve the anti-fade property & deeper colour absorption.

Apache HTTP Server Vulnerabilities: October 2021 - vulnerability database
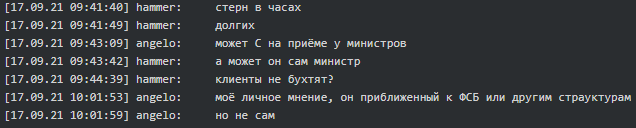
Conti Leaks: Examining the Panama Papers of Ransomware, Tre - vulnerability database
vnet/fixtures/2samples.json at master · Meelfy/vnet · GitHub
html-tweaker/Facebook.html at master · uniba/html-tweaker · GitHub

如何使用C++ 在Word文档中创建列表_51CTO博客_java创建word文档
codex_cli/tokenizer.json at main · moyix/codex_cli · GitHub
ntdf-tools/gamefile_reader.html at master · monster860/ntdf-tools · GitHub
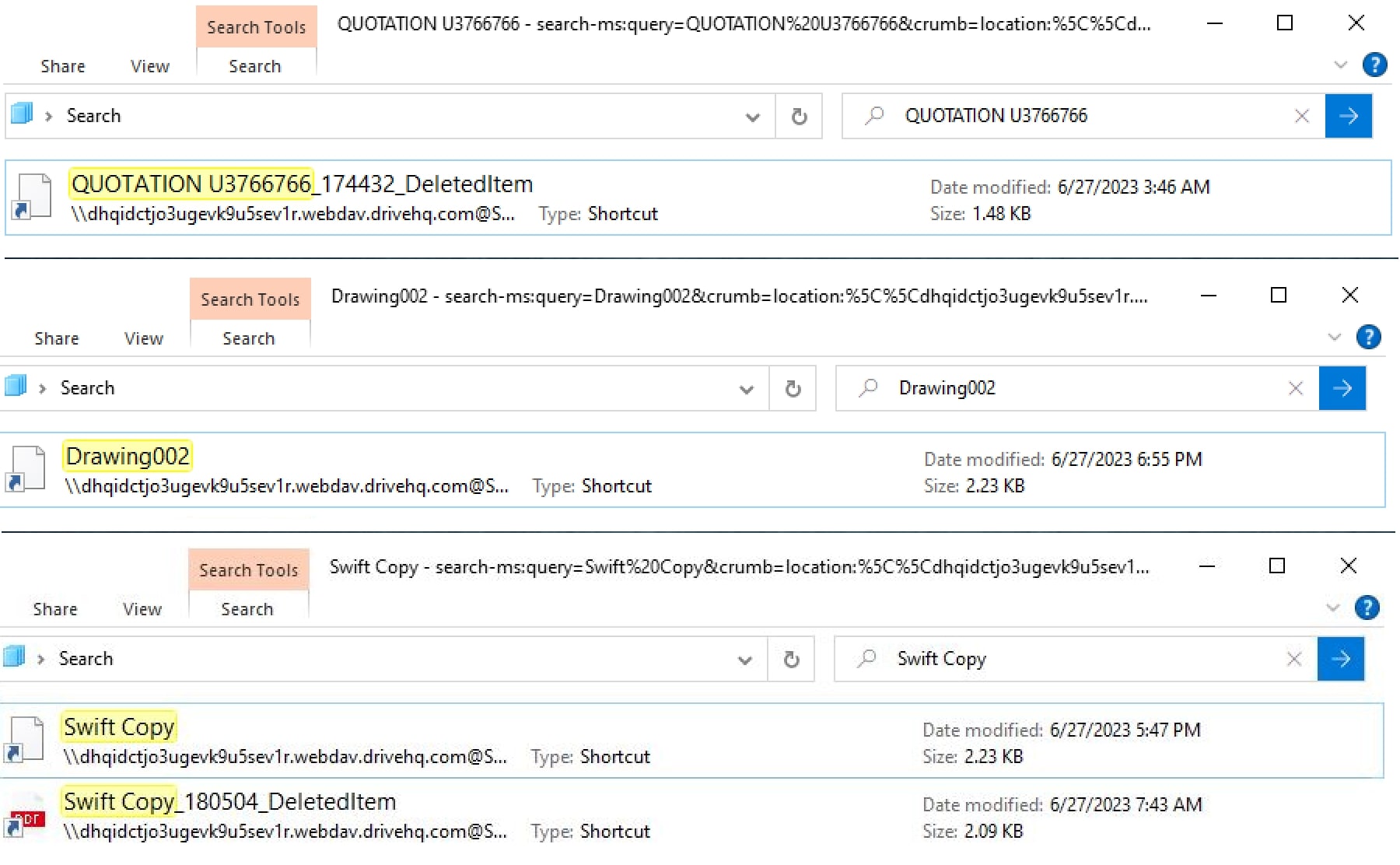
Beyond File Search: A Novel Method - vulnerability database

Cl0p ransomware gang claims first victims of the MOVEit vuln - vulnerability database

Special Characters Cheat Sheet, PDF, Written Communication
SciREX/docs/train_docs/0523e14247d74c4505cd5e32e1f0495f291ec432.json at master · allenai/SciREX · GitHub
website/links.json at gh-pages · academia-de-ursarie/website · GitHub